This page describes step by step how to build a private virtual network with Solaris 11 zones.
Solaris 11 zones which operate in a private virtual network have the following advantage
- They allow to quickly configure complex distributed applications in a private network
- The network and the zones are completely hidden inside a Solaris 11 system
- No coordination with network administration in regards of IP addresses, router configurations etc. is needed
The required resources are
- an Oracle Solaris 11 server without sufficient memory, disk and CPU resources to operate the applications needed. The zones overhead will be most likely not relevant
- root privileges to your Oracle Solaris 11 server
- an IPS server in the network of your Oracle Solaris 11 server. It will be needed to install zones on the fly
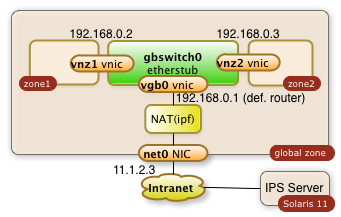
This step-by-step tutorial will show how to configure an internal network with zones as shown in the diagram below:
You will learn how to...
- create a virtual switch (gbswitch0) inside your Oracle Solaris 11 servers
- virtual network interfaces (vgb0, vnz1, vnz2) which will be attached to the virtual switch
- create zones which will use the virtual switch
- configure the routing to keep all communication inside your Oracle Solaris server
- configure a network address translation (NAT) which allow your internal zones to access external services like DNS
- configure a reverse proxy for the public network interface. This reverse proxy will allow to access internal web applications through the already existing public network interface
- access your internal zones through the intranet with ssh tunneling through the public IP address
To summarize it: This is your personal private lab in a box. Some call it a cloud.
All required operations can be performed with a few scripts as root from the global zone. There are no extra licenses required to operate your cloud in a box...
References:
- Oracle Documentation Planning and Designing a virtual network
- Nicholas Droux' Blog: Private virtual networks for Solaris xVM and Zones with Crossbow
The three sections of the how-to guide:
- Printer-friendly version
- Log in to post comments
- 8518 views